Thanks to COVID-19, virtual work environments are here to stay. But while employees may be safe and sound working from home, the work data and proprietary information on the computers they use at home may not be so safe! Why not? Because work-from-home environments often lack the same cybersecurity safeguards found in an office setting… which translates into exploitable weaknesses and vulnerabilities. To make matters worse, many businesses are unaware of these new sets of risk – and employees are likely unaware, too.
On May 12, Bold Business hosted Keeping Virtual Work Environments Secure: Really Smart Cybersecurity Tips for Businesses, a webinar that featured the expert insight of Master Security Consultant Steven Wiegelt.

Wiegelt covered five different areas where businesses face risks:
- Tools and Software
- Network
- Security Awareness Training
- Policy and Procedures
- Intellectual Property Protection
But first, Wiegelt illustrated some of the more obvious dangers that come with working outside of the office.
The Perils of Working from Home
Smart businesses met the challenges of lockdown by sending their employees home with laptops and (hopefully) seamlessly maintaining continuity with plenty of video conferences. But according to Wiegelt, there are still plenty of perils businesses and employees alike face. They include:
- A blended personal and work life – when the line between home and office gets blurred, productivity and security awareness can suffer
- Device sprawl – too many devices means too much confusion
- Shared workspace – ever have to tell your kid not to mess around with your laptop?
- A home WiFi that may not be secure or even strong enough to support business needs
- Lack of IT support – who are you going to call when you have issues?
What can you do to combat these perils?
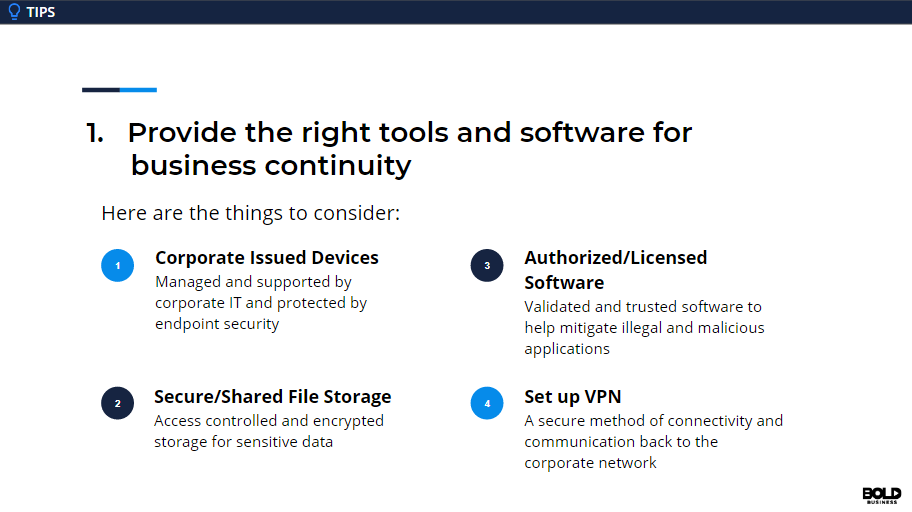
The Right Tools
Every business needs the right tools to function properly, and for a business in a work-from-home posture, that means software for managing workflow and sensitive information, storing sensitive data, management controls for monitoring access and activity.
Wiegelt’s advice:
- Provide corporate-issued devices
- Maintain secured file storage
- Use authorized and licensed software
- Set up a VPN (virtual private network)
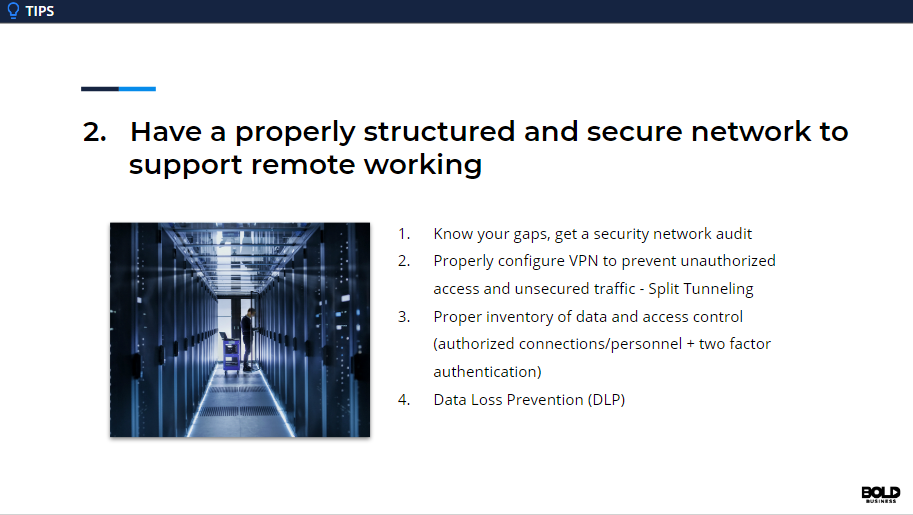
Keep Your Network Secure
For some, simply figuring out how to input a WiFi password and logging on to a network is a victory. But the bar for success must be kept much higher when business data and proprietary information is at stake: a network must be secure!
According to Wiegelt, the dangers of an unsecured include loss of productivity, data leakage, limited resource availability, and bandwidth issues.
His advice:
- Get a security audit to learn your gaps
- Make sure your VPN is properly configured
- Make an inventory of your data and who has access to it
- Engage in Data Loss Prevention
The Weakest Link
The numbers don’t lie. While a business can make sure all their technical ducks are lined up in a row, statistics show that 90% of data breaches are caused by human error!
To manage this particular area of risk, Wiegelt advocated aggressive security awareness training.

The training itself must be as real as possible (meaning, it simulates a real world attack).
It should also be consistent. In other words, security awareness training that occurs once every leap year might not cut it.
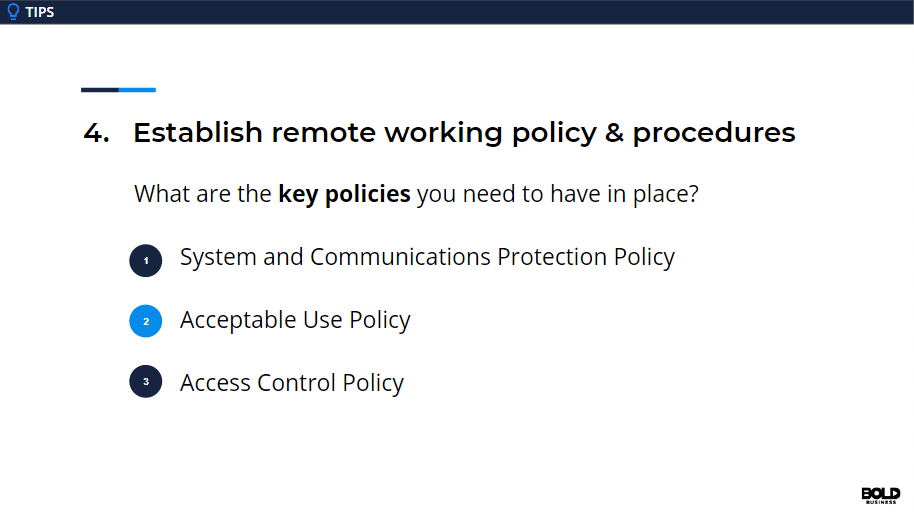
The Need for Policies and Procedures
Of course, a strong training program is all well and good, but the other side of the “people management” coin is an established set of policies and procedures.
Wiegelt pointed out three key policies a business needs to have in place for employees who work from home (although it would be great if these policies existed for those working in offices, too). They are:
- A System and Communications Protection Policy
- An Acceptable Use Policy
- An Access Control Policy
Wiegelt noted that some businesses – like those that deal with sensitive healthcare information or financial data – have regulatory requirements involving putting policies in place.

Protecting Intellectual Property
At the end of the day, protecting data is about protecting intellectual property.
For that, Wiegelt laid out for key tips:
- Use an Antivirus on your computer
- Set up a Firewall to protect your network from incursion
- Utilize Secure Storage for files
- Employ Authentication protocols to Secure Terminals

If you missed the webinar, you can watch it here.